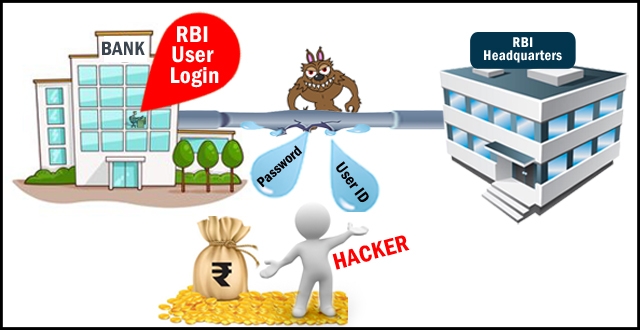
Very recently we came across a phishing site which emulates RBI and steals the login credentials of RBI users. However, it seems like a spear-phishing attack targeting the users of a specific bank.
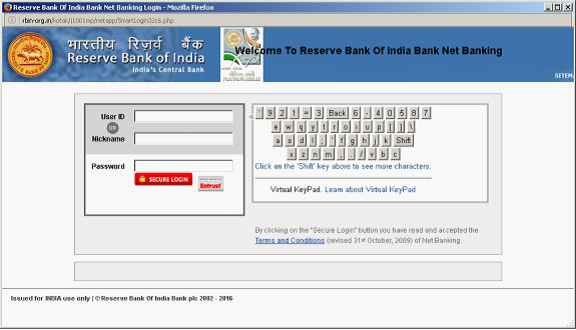
The perpetrators have taken the efforts of not just registering the domain rbin-org[.]in, but have also cloned the entire RBI site up-to the first level of the available links. In previous instances we have observed RBI phishing attacks which try to emulate the login panels of almost all the existing banks . This seems to be different as its not targeting the normal Banking Users at large but is targeting specific users.
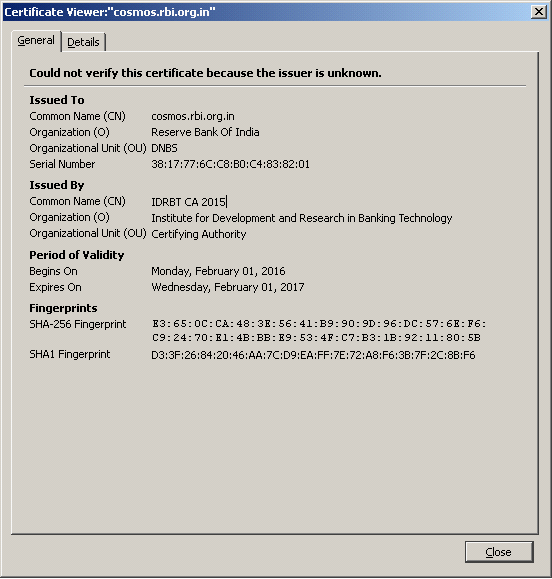
It is also to be noted the the fake site doesn’t have a SSL Certificate, however even RBI’s official website has a broken SSL Certificate.

The Phishing Site


Detection Algorithms
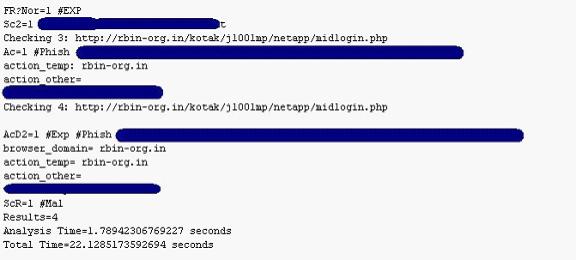
We at eScan invest our resources to come up with algorithms which weed out the human factor and try to merge the human intelligence with heuristic , computer assisted algorithms. The first one being Smart Phishing Filter or SURL , about which we have written a great detail with live examples about the success of it. SMART Phishing Filter / SURL detects these phishing links with accuracy.
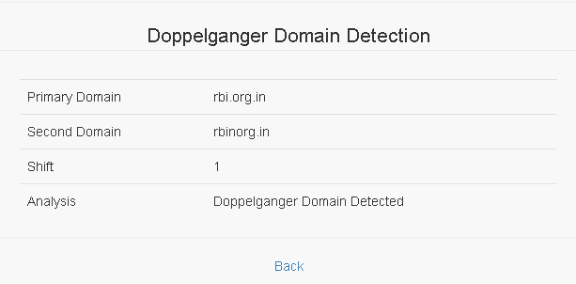
The other experimental algorithm is the Doppelganger Domain Detection, which is more about the detection of typo-error type domains which most of the time fail to get detected at all levels.
The results of both the algorithms have been shown in their raw format.
SMART Phishing Filter
Readers may choose to read more about SURL / SMART Phishing Filter and Doppelganger Domain Detection over here.
Phishing-Analyzer
http://blog.escanav.com/2012/08/13/surla/
http://blog.escanav.com/2012/09/17/malwaremustdie-bhek-v2/
http://blog.escanav.com/2012/10/16/to-believe-or-not/
http://blog.escanav.com/2012/10/30/citibank%e2%80%93phishing/
http://blog.escanav.com/2012/11/20/surla-2/
http://blog.escanav.com/2012/11/27/surl-msf-set/
http://blog.escanav.com/2013/01/15/surl-tweets-and-phishing/
http://blog.escanav.com/2013/03/12/escan-14-dynamic-phishing-filter/
http://blog.escanav.com/2013/04/26/phishing-blocked-by-htaccess/
http://blog.escanav.com/2013/06/17/facebook-phishing-attack/
http://blog.escanav.com/2013/12/03/india-phishing-inc/
http://blog.escanav.com/2014/01/24/phishing-customer-satisfaction-survey/
Doppelganger Domain Detection
http://blog.escanav.com/2016/10/07/bec-business-email-compromise/








