Business Email Compromise is commonly known as BEC, and much has been written and discussed about it, you may choose to revisit the below mentioned links :
- https://www.ic3.gov/media/2016/160614.aspx
- http://krebsonsecurity.com/tag/business-email-compromise/
- https://www.fbi.gov/file-repository/email-compromise_508.pdf
There are various methods by way of which a compromise is achieved by the criminals
1: Doppelganger domains or Typo squatting of domains
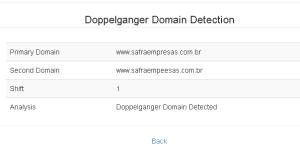
Doppelganger domains or Typo squatting domains are those domains which are very much similar to the original domain however there is a slight change in the spelling. Recently a group of researchers, typo-squatted a couple of hundred domains, deployed a mail server to receive the mails and the end-result – they were able to capture almost 2GB of emails which were sent by unsuspecting users who had made a typo mistake in spelling out the domain, while sending the email.
Eg.
FACEBOOK.COM or FACEB00K.COM
TWITTER.COM or Tvvitter.com
WWW.SAFRAEMPRESAS.COM.BR or WWW.SAFRAEMPEESAS.COM.BR
ASIANPAINTS.COM or ASlANPAINTS.COM
These are real-world examples and at some point in the past have been used to carry out attacks and its difficult to comprehend which is the real site and which one is the fake.
2: ReplyTo pointing to a different email-id
When emails are being spoofed, there is a high degree of probability that “REPLY-TO” field of the email might be pointing to the criminals own email-id .
3: Message Body / Subject
The entire gambit of enticing the end-user lies in this section. The content of the mails are highly personal, written with an air of authority which forces the reader to comply. We may also come across masqueraded links which may point either to phishing sites or to a malware.
From a holistic point of view everything about emails is very risky. In order to combat such mails, vendors have come up with very unique solutions viz. Grey Listing, SURBL checkups , MX / DKIM checks / verifications . Mail Server Administrators also go to the extent of enabling authentication and allowing the authenticated users to send emails. However, with all these checks and balances in place we still have to bear the brunt of BEC.
In order to combat Typo squatting / Doppelganger Domains, readers may choose to visit this link (Doppelganger Domain Detection Algorithm) which provides an interface to verify whether there is any difference between the two domain-names or not.
This is a algorithmic approach to tackle the issue, however it is to be noted that there is a need for at least one domain-name to be the real one. Share your inputs/thoughts/ideas as a comment in this blog-post.
Where can this be deployed?
It’s at the mail-server where this needs to be implemented, since Mail-Server has the List of domains for whom it is supposed to receive the mails. And it is over here , at the email gateway level that you can detect such attempts and tag them accordingly.
One thing is for sure that this algorithm cannot be used in its present form, for comparing Sender User-ID, since this will require an additional layer of data-set which specifically maintains the user-id list. However, if you can overcome this factor then, sky is the limit.
Moreover, you may also choose to down the ESAT toolset and based on the results either fortify your mail-server or as a developer, choose to address the pain-points raised by this tool. (Email Server Audit Tool).
The next blog-post would be about – Why I believe that an algorithm-based approach is best suited to tackle this.
Till then, Stay Safe !!!