Snippets of IT security news An update on recently published IT security news is in snippets here. Get resourceful updates from eScan on what’s happening over the security industry. Wi... Read more
Microsoft has released patches for 60 vulnerabilities with some of them being actively exploited in the wild. Furthermore, Adobe has released patches which addresses three vulnerabilities. T... Read more
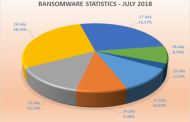
Ransomware updates Mid-Week of Week No. 30 saw the most attacks being averted, however, unlike previous weeks we saw a surge of malware-laced domains/Command and Control Servers being contac... Read more
The world has come a long way since the invention of computers decades back. Today virtually we live everyday breathing technology, like oxygen for the body. In recent times technology has a... Read more
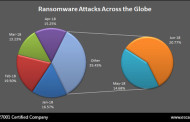
According to a threat report revealed by eScan, the state of Maharashtra has recorded the highest number of Ransomware attacks in the month of June 2018. Other states included in the list we... Read more